OCR
Your school or university
Improve your search results. Select your educational institution and subject so that we can show you the most relevant documents and help you in the best way possible.
Ok, I understand!
Unit 14 Software engineering for business
5. Communication, Homeostasis & Energy
: 1.1 The Circular Flow of Income
\\\'Echo\\\' - Christina Rossetti
0CR AS LEVEL PSYCHOLOGY PAPER 2 MS
1-6
1. Foundations in biology
1.1
1.1.1 Structure and Function of the Processor
1.1.2 Types of Processor
1.1.3 Input and Output Storage
1.2
1.2.2 Applications Generation
1.3
1.4
1.5
1445-1509: Lancastrians, Yorkists and Henry VII
1964 election essay plan
2 - basic components of living systems
2. Foundations in biology
2.1 Cell Structure
2.1.1 Basic components of living
2.1.1 Biological Molecules
2.1.1 Cell Structure
2.1.1 Cells and microscopy
2.1.2 and 2.1.3 Biological Molecules, Nucleotides and Nucleic Acids
2.1.2 Water and its importance in plants & animals
2.1.2. Biological Molecules
2.1.3 Proteins and enzymes
2.1.4 Enzymes
2.1.4 Nucleic acids
2.1.5 Biological Membranes
2.1.6 Cell Division
2.1.6 Cell Division, Cell Diversity and Cellular Organisation
2.2 Biological Molecules
2.2.1 The heart and monitoring heart function
2.2.2 Transport systems in mammals
2.2.3 Gas exchange in mammals and plants
2.2.4 Transport systems in plants
2.3 Nucleic Acids
2.4 Enzymes
2.5 Biological Membranes
2.6 Cell Division, Diversity ad Differentiation
2021 locked papers
2022 papers and markschemes
2023 papers and markschemes
20th Century: Religious Language
2V0-21.20 PDF Dumps
3.1 Exchange Surfaces and Breathing
3.1.1 Exchange and Transport
3.1.2 Transport in Animals
3.1.3 Transport in Plants
3.2 Transport in Animals
3.3 Transport in Plants
4
4.1
4.1.1 Communicable Diseases, Disease Prevention and the Immune System
4.1.1: Basic Concepts of Organic Chemistry
4.1.2 Alkanes and 4.1.3 Alkenes
4.2.1 Biodiversity
4.2.1: Alcohols and 4.2.2: Haloalkanes
4.2.2 Classification and Evolution
5. Communication, Homeostasis & Energy
5.1 Communication and Homeostasis
5.1.1 and 5.1.2
5.1.1 and 5.1.2: How Fast/How Far
5.1.3
5.1.3 Acids and Buffers
5.1.4
5.1.4 Hormonal Communication
5.1.5
5.1.5 Plant and Animal Responses
5.2 Respiration
5.2.1
5.2.1 and 5.2.2 Enthalpy and Entropy
5.2.1 photosynthesis
5.2.2
5.2.3: Redox and Electrode Potentials
5.3 Neuronal Communication
5.3.1 Transition Elements
5.4 Hormonal Communication
5.6 Photosynthesis
5.7 Respiration
6 mark essays
6.1 Cellular Control
6.1.1
6.1.1 Aromatic Compounds
6.1.1 Intro to Aromatic Compounds
6.1.2
6.1.2 Carbonyl Compounds
6.1.3
6.2 Cloning and Biotechnology
6.2 Patterns of Inheritance
6.2.1
6.2.1 Amines
6.2.1 Cloning and Biotechnology
6.2.2 Amides and chirality
6.2.3 Polyesters and polyamides
6.2.5 Organic synthesis
6.3 Manipulating Genomes
6.3.1
6.3.2
601/4260/1
601/4799/4
9990
A LEVEL CHEMISTRY 2021
A level Chemistry
A Level GCE Economics H460/02: Macroeconomics
A Level GCE Physics A H556/02
A Level Biology
A level chemistry
A LEVEL Chemistry A H432/03: Unified chemistry
A LEVEL COMPUTER SCIENCE PAPER 2 H446/02 JUNE 2022
A Level Economics H460/01 Microeconomics
A Level Economics H460/02
A Level Economics H460/03 Themes in economics
A Level GCE Computer Science H446/02: Algorithms
A LEVEL GCE Physics
A LEVEL GCE Physics A H556/03: Unified physics
A LEVEL GCE Psychology H567/01
A LEVEL GCE Psychology H567/02
A level History
A Level Macro Economics
A LEVEL Mathematics B MEI
A LEVEL Mathematics B MEI H640/01
A LEVEL Mathematics B MEI H640/03
A level notes
A Level Physics A H556/01
A Level Physics A H556/02 Exploring physics
A Level Physics A H556/03 Unified physics
A Level Psychology H567/02 Psychological themes
A Streetcar Named Desire
A View From the Bridge
A_Level_Economics_Question _bank
A-level BIOLOGY
A-Level Computer Science
A-Level Past Paper Tracker
A* Level - All of Chemistry
A2 Capacitance
A2 Circular Motion
A2 Electric Fields
A2 G325 - Critical Perspectives in Media
A2 Gravitational Fields
A2 Magnetic Fields
A2 Unit 4 - Listening, Reading and Writing 2
A2 Unit 4 F724 - Spanish Listening, Reading and Writing 2
A2 Unit AH3 F393 - Greek History: conflict and culture
A2 Unit AH4 F394 - Roman History: the use and abuse of power
A2 Unit CC10 F390 - Virgil and the world of the hero
A2 Unit CC8 F388 - Art and Architecture in the Greek World
A2 Unit CC9 F389 - Comic Drama in the Ancient World
A2 Unit F014 - Management Accounting
A2 Unit F214 - Communication, Homeostasis and Energy
A2 Unit F215 - Control, Genomes and Environment
A2 Unit F216 - Practical Skills in Biology 2
A2 Unit F248 - Strategic decision-making
A2 Unit F249 - A business plan for the entrepreneur
A2 Unit F293 - Marketing
A2 Unit F294 - Accounting
A2 Unit F295 - People in Organisations
A2 Unit F297 - Strategic Management
A2 Unit F324 - Rings, Polymers and Analysis
A2 Unit F325 - Equilibria, Energetics and Elements
A2 Unit F326 - Practical Skills in Chemistry
A2 Unit F334 - Chemistry of Materials
A2 Unit F335 - Chemistry by Design
A2 Unit F336 - Chemistry Individual Investigation
A2 Unit F583 - Economics of Work and Leisure
A2 Unit F584 - Transport Economics
A2 Unit F585 - The Global Economy
A2 Unit F633 - Global Cinema and Critical Perspectives
A2 Unit F653 - Culture, Language and Identity
A2 Unit F654 - Media Language
A2 Unit F673 - Dramatic Voices
A2 Unit F674 - Connections across Texts
A2 Unit F763 - Global Issues
A2 Unit F764 - Geographical Skills
A2 Unit F794 - Environmental Geology
A2 Unit F795 - Evolution of Life, Earth and Climate
A2 Unit F853 - Contemporary US Government and Politics
A2 Unit F854 - Political Ideas and Concepts
A2 Unit F855 - US Government and Politics
A2 Unit F856 - Political Ideas and Concepts in Practice
A2 Unit F919 - Care practice and provision
A2 Unit F920 - Understanding human behaviour and development
A2 Unit F921 - Anatomy and physiology in practice
A2 Unit F922 - Child development
A2 Unit F923 - Mental-health issues
A2 Unit F924 - Social trends
A2 Unit F925 - Research methods in health and social care
A2 Unit F965 - Historical Interpretations and Investigations
A2 Unit F966 - Historical Themes
A2 Unit F987 - Historical Significance
A2 Unit G063 - ICT Systems, Applications and Implications
A2 Unit G153 - Criminal Law
A2 Unit G154 - Criminal Law Special Study
A2 Unit G155 - Law of Contract
A2 Unit G157 - Law of Torts
A2 Unit G356 - Historical and Analytical Studies in Music
A2 Unit G453 - Principles and concepts across different areas of Physical Education
A2 Unit G454 - The improvement of effective performance and the critical evaluation of practical activities in Physical Education
A2 Unit G484 - The Newtonian World
A2 Unit G485 - Fields, Particles and Frontiers of Physics
A2 Unit G486 - Practical Skills in Physics 2
A2 Unit G542 - Core Studies
A2 Unit G543 - Options in Applied Psychology
A2 Unit G544 - Approaches and Research Methods in Psychology
A2 Unit G673 - Power and Control
A2 Unit G674 - Exploring Social Inequality and Difference
A2 Unit H403/31 Greek Religion
A2 Unit Y319: Civil RIghts in the USA
A2 Units F985 and F986 - Historical Controversies
A452
A453 Encryption
Academic Development
Access to Justice
accoutancy
Acids and Redox
Acids, Bases and pH
Advanced Energetics
Aeneid
African American Civil Rights 1865- 1992
African American Civil Rights 1865-1992
African Kingdoms
African Kingdoms c1400-c1800
Aggregate Demand and Aggregate Supply
Alcohols, Organic Chemistry
Algorithms and programming
Alkanes, Organic Chemistry
Alkenes, Organic Chemistry
all
All content
All modules
All Past Papers
All the modules
Alternative Dispute Resolution
American Civil Rights 1865-1992
American Depth Study
American Literature
American Revolution
Amines
Amines, Amides and Amino acids
Amount of Substance
anatomy and physiology
Anatomy and Physiology Unit 9
Ancient Philosophical Influences
animal and plant cells
Animal response
Animal Transport
Anthropology
Antibiotic Resistance Summary
Applied Anatomy and Physiology
Applied Anatomy and Physiology
Applied Anthropology
Applied Psychology notes
Applied Science
applying anthropology
Arguments for the Existence of God: Observation
Arguments On Observation / Cosmological Argument
Aristotle
Aromatic Compounds
Aromatics
Art
Art and Design: Fine Art
Art history collecting cultures
AS
AS 2-Basic components
AS Acids and REDOX
As and A level
AS Biology
AS BIOLOGY MIND MAPS
AS Chemistry
AS Foundation in Biology- Cell ultrastructure
AS G322 - Key Media Concepts
AS Law Making
AS Level Biology A Breadth in biology September 23 2020
AS LEVEL BIOLOGY B PAPER 2 H022/02
AS level Business
AS Level Chemistry
AS Level Chemistry A H032/01 Breadth in chemistry September 23 2020
AS Level Chemistry A H032/01: Breadth in chemistry
AS Level Chemistry A H032/02 Depth in chemistry
AS LEVEL PSYCHOLOGY PAPER 2
AS level/Yr 1
AS Micro Economics
AS Past Paper Tracker
AS Unit 2 F702 - Listening, Reading and Writing 1
AS Unit AH1 F391- Greek History from original sources
AS Unit AH2 F392 - Roman History from original sources
AS Unit CC2 F382 - Homer\'s Odyssey and Society
AS Unit CC2 F382 - Homer\\\\\\\'s Odyssey and Society
AS Unit CC4 F384 - Greek Tragedy in its context
AS Unit CC6 F386 - City Life in Roman Italy
AS Unit F211 - Cells, Exchange and Transport
AS Unit F212 - Molecules, Biodiversity, Food and Health
AS Unit F213 - Practical Skills in Biology 1
AS Unit F241 - Recruitment in the workplace
AS Unit F246 - Financial providers and products
AS Unit F247 - Understanding production in business
AS Unit F291 - An introduction to Business
AS Unit F292 - Business Functions
AS Unit F321 - Atoms, Bonds and Groups
AS Unit F322 - Chains, Energy and Resources
AS Unit F323 - Practical Skills in Chemistry 1
AS Unit F331 - Chemistry for Life
AS Unit F332 - Chemistry of Natural Resources
AS Unit F581 - Markets in Action
AS Unit F582 - The National and International Economy
AS Unit F671 - Speaking Voices
AS Unit F672 - Changing Texts
AS Unit F761 - Managing Physical Environments
AS Unit F762 - Managing Change in Human Environments
AS Unit F791 - Global Tectonics
AS Unit F792 - Rocks - Processes and Products
AS Unit F851 - Contemporary Politics of the UK
AS Unit F852 - Contemporary Government of the UK
AS Unit F910 - Promoting quality care
AS Unit F911 - Communication in care settings
AS Unit F912 - Promoting good health
AS Unit F913 - Health and safety in care settings
AS Unit F914 - Caring for people with additional needs
AS Unit F915 - Working in early-years care and education
AS Unit F916 - Health as a lifestyle choice
AS Unit F917 - Complementary therapies
AS Unit F918 - Caring for older people
AS Unit F961 - British History Period Studies
AS Unit F962 - European and World History Period Studies
AS Unit F963 - British History Enquiries
AS Unit F964 - European and World History Enquiries
AS Unit G061 - Information, Systems and Applications
AS Unit G151 - English Legal System
AS Unit G152 - Sources of Law
AS Unit G352 - Composing 1
AS Unit G481 - Mechanics
AS Unit G482 - Electrons, Waves and Photons
AS Unit G483 - Practical Skills in Physics 1
AS Unit G542 - Core Studies
AS Unit G671 - Exploring Socialisation, Culture and Identity
AS Unit G672 - Topics in Socialisation, Culture and Identity
AS Unit Y221 Democracy and Dictatorship in Germany
AS Units F981 and F982 - Historical Explanation
AS/ A-Level Philosophy of religion
Assessment Objective 1
Assessment Objective 2
Assessment Objective 3
Assessment objective 4
Astrophysics and Cosmology
Atomic Structure and Bonding
Atoms, Ions and Compounds
Attempts
Augustine and Human Nature
B1-B6
B2.1.2 Biological molecules
B2.1.3: Nucleotides and nucleic acids
B2.1.4: Enzymes
B2.1.5: Biological Membranes
B2.1.6: Cell division
B3.1.1: Exchange and transport
B3.1.2: Transport in animals
B3.1.3: Transport in plants
B4.1: Disease
B4.2.1: Biodiversity - sampling
B4.2.2: Classification and Evolution
B5.1.1: Communication and homeostasis
B5.1.5: Animal responses
B5.1.5: Plant responses
B5.2.1: Photosynthesis
B5.2.1: Respiration
B6.3.1: Ecosystems
BANKING 101
Basic components of living systems
Basic Components of Living things
Basic concepts and hydrocarbones
Benzene and Phenols
Biodiversity
Biodiversity 4.2.1
Biodiversity, Evolution and disease
Biological Membranes
Biological Membranes and Cell Division
Biological Molecules
Biological molecules - water
Biological Molecules + Enzymes
Biological Molecules and Simple Carbohydrates
Biological Molecules- Carbohydrates
Biological Processes
Biological Psychology
Biology
biology a
biology1102
Biomechanics
Biotechnology
Blood Vessels
Bonding and structure
Breadth In Physics
Breakfast at Tiffany\\\'s and A Streetcar Named Desire
Breakfast at Tiffany\\\\\\\'s and A Streetcar Named Desire
britain 1930 - 1997
Britain 1930 1997
Britain 1930-1997
Britain 1930—1997
Britain 1945-1997
Britain and Ireland 1791—1921
Britain History
British History
British Politics
Buddhism in The East
Buffers
Buffers and buffer calculations
BUS 22
business
Business Decisions
Business ownerships
Business Structure
capacitance
Carbohydrates
Carbon oxygen compounds and reactions
Cardiovascular and respiratory system
Cardiovascular system
Case Studies
Cell Biology
Cell Cycle
Cell division
Cell Division & Organisation
Cell Division and Organisation
Cell division, diversity & organisation
Cell Division, Diversity and Differentiation
Cell divisions
Cell Membranes
Cell structure
Cells
Cellular Control
Cellular control 6.1.1
Change management
Changing Nature of Warfare
Changing Nature of Warfare 1792-1945
Changing Spaces Making Places
Changing Spaces Making Places - Human Geography
Changing Spaces, Making Places
Changing spaces; making places
Changing Spaces; Making Places Questions
Chapter 10 4.2.2 Classification and Evolution
Chapter 12 4.1.1 - Communicable Diseases
Chapter 13 Neuronal Communication
Chapter 2
Chapter 2 Atomic structure and Isotopes
Chapter 2 Atoms, Ions and Compounds
Chapter 22
Chapter 23
Chapter 25
Chapter 29
Chapter 9- Exchange in plants
Characteristics of Contemporary Processors
Cheatsheets
CHEM 211
chem lab
Chemical tests
Chemistry
chemistry A
Child Language Acquisition
child psychology
China and it\\\'s rulers
Christian Moral Action
Christian Moral Principles
Christian Thought
Chromatography
Chromatography and Mass Spec, Chapter 29
Circular and Harmonic Motion
Circular Motion
Civil Courts
Civil Rights
Civil Rights 1865-1992
Civil Rights America 1865-1992
Civil Rights in America
civil rights in the usa
Civil Rights in the USA : Trade Unions
Civil Rights in the USA : Women
Civil Rights in the USA 1865 - 1992
Civil Rights in the USA 1865-1992
Civil Rights in the USA 1865–1992
Civil Rights in the USA Thematic Study
Civil Rights in the USA, 1865-1992
Civil Rights in the USA: African Americans
Civil Rights in the USA: In-depth studies
Civil Rights in the USA: Native Americans
Civil rights Y319
Classical Greek
Classification & evolution 4.2.2
Classification and evolution
Climate Change
Cloning
Cloning & Biotechnology 6.2.1
Cloning and Biotechnology
Coastal Environments
Coastal Landscapes
Coasts
Cognitive Psychology
cold war in europe
Communicable Diseases
Communicable diseases, prevention & immune 4.1.1
Communication & Homeostasis 5.1.1
Communication methods
Communication, homeostasis and energy
Comparative and contextual study
Comparative and Contextual Study WTN
COMPLETE AS and A2 Course
Component 1,USA 1919—1948: The people and the state
Component 2, Power: Monarchy and democracy in Britain c. 1000 — 2014
Components of a Computer and their uses
Composition & Theory
Comprehensive Guide
Computational Thinking, Algorithms, & Programming
Computer
COMPUTER SCIENCE
computer science revision notes
Conscience
Conservation and Preservation
Contemporary Issues in Sport
Contractual Terms
Coordination and Homeostasis
Core Organic Chemistry
Coursework
Crime and Deviance
Crime and globalisation
Criminal law
criminal law study guide
Criminal Liability
Criminal Processes (Appeals, Pre-Trial, Categories
Critical Approaches
Critical Response in Writing
Crossing membranes
Daphnia Practical - 11.2
Data Analysis
Data Types
Date base
DCT
Death and the afterlife
Debates in contemporary society
Defences
Delegated Legislation
Democracy and Dictatorships in Germany 1919-1963
Democracy and the Athenians
DES-5121 PDF Dumps
Design
Design and Technology
Design argument
Design Engineering
Design Technology
Developing fuels
Developing metals
Development in Christian Thoughts
Development of Christian Thought
Development of Practical skills in Biology
Developmental Psychology
Developments in Christian Thought
Dilution plating
Dimensions of linguistic variation
Discharge
Disease
Disease Dilemas
Disease Dilemmas
diseases
Dissection
DJ Skills
DNA Profiling Summary
DNA structure
Dracula
Drama
Drama and poetry pre-1900
Dystopia
Dystopian Fiction
Dystopian Literature
Earth\\\'s Life Support Systems
Earth\\\\\\\'s Life Support Systems
Economic Duress
Ecosystems
Ecosystems 6.3.1
Edexcel A Level Biology Paper 1 Mark Scheme 2022
Education
Educational Policy
Effect of Exercise on Pulse Rate
Elasticity
Electricity
Electronic Structure
Electrons and Bonding
Elements from the sea
Elements of a Crime
Elements of crime writing
Elements Of Life
Elizabeth I
Emergence and Evolution of Modern Sport
Emergence and Evolution of Sport
Employment Law
ENGINEERIN 1058
ENGINEERING
engineering financial technology
England : the early Tudors
England 1445-1509
England 1445–1509:Lancastrians,Yorkists + HenryVII
England 1485–1558: the Early Tudors
England 1547–1603: the Later Tudors
English Language
english literature
Enterpenuership
Enthalpy
Enthalpy Changes
Enthalpy, Entropy and Free Energy
Entire Course
Entire specification
Environmental Ethics
Environmental Management
Environmental Psychology Paper 3
Enzymes
EPQ
Equilibria
Equilibria, Haloalkanes and Alcohols
Ethics
Evolving Media
Exam paper
Exam Questions
exam test paper
Exchange & Transport
Exchange and Transport
Exchange Surfaces
Exchange Surfaces 3.1.1
Excretion
Excretion 5.1.2
Excretion and the kidneys
Exercise Physiology
Exploring Language
Fatal Offences
Feedback
Field-Service-Lightning-Consultant PDF Dumps
film and literature
Film History
Final Project
First year
Fiscal policy
Food tests
Forces
Forces and motion
Formation
Foundation of Chmeistry - MODULE 2
foundations in biology
foundations in biology- enzymes
Foundations in Chemistry
Foundations in Physics
Foundations of physics
Four Noble Truths
France in Revolution: 1774-1815
Frankenstein
Frankenstein, Mary Shelley
French Revolution
From Pitt to Peel: Britain 1783-1853
Full course
Functionalism - Families and Households
Fundamental Organic and Alkenes
Fundamentals of IT
further Mathematics
Future of Food
G400
G571 - AS Philosophy of Religion
G572 - AS Religious Ethics
G575 - AS Developments in Christian Theology
G578 - AS Islam
G581 - A2 Philosophy of Religion
G582 - A2 Religious Ethics
G585 - A2 Developments in Christian Theology
G586 - A2 Buddhism
Gas Exchange in Animals and Insects
Gas Exchange Systems and Breathing
GCE AS LEVEL PSYCHOLOGY
GCE Mathematics B MEI H640/03
GCE A Level Economics H460/01
GCE A LEVEL Chemistry A H432/03: Unified chemistry
GCE A LEVEL Economics H460/03
GCSE
GCSE ENGLISH LITERATURE
GCSE STATISTICS 8382/2H HIGHER TIER PAPER 2
Gender
Gender and society
Gender and theology
Gene Regulation Summary
Gene Therapy Summary
general defence evaluation essay
General Defences
Genetic Engineering Summary
Genetics of Living Systems
Genetics, Evolution and Ecosystems
Geographical Debates
Geographical Debates Case Studies
Geographical Debates - Hazardous Earth
glaciated landscapes
Global Migration
Global Migration Questions
Global sporting events
globalisation
globalisation and digital social world
Globalisation of sport
Gothic
Gothic Literature
grammar
Grammar and Vocabulary
Gravitational Fields
Greek Art
Greek Religion
Greek Religion and Democracy
Greek Theatre
gross negligence manslaughter
H020 and H420
H022/02 Biology in depth
H022/02: Biology in depth
H046-01
H156/02
H173 - Philosophy of Religion
H407/12 - The Politics and Culture of Athens
H407A
H408/11 The World of the Hero
H408/11 World of the Hero
H408/21 Greek Theatre
H408/32 Love and Relationships
H408/33 Politics of the Late Republic
h418
H418/04 – The nature of law and the law of contrac
H420
H432
H432/02
H432/03
H446
H466
H472/03
H481/01 Physical Systems
H573 - Philosophy of Religion
H573 - Religion and ethics
H573/01 - Philosophy of Religion
H573/01 Philosophy of Religion
H573/02 Religion and Ethics
H573/03 - Developments in Christian Thought
H573/03 Developments in Christian Thought
H580
H580/02 Paper 2 Social inequalities
H580/03 Paper 3 Debates in contemporary society
Haloalkanes Organic Chemistry
Hamlet
Handmaid\\\'s Tale
Haydn, Mozart and Beethoven
Hazardous Earth
Hazardous Environments
Health and Disease
Health and science
HEALTH AND SOCIAL CARE BTEC LEVEL 3 STUDY GUIDE
Health promotions
HESI 1 - V1 and V2 REVIEW - Health Assessment 1
History a level paper 3
History IGCSE Section 2
History Paper 1
History Paper 2
History Paper 4
HO32
Homeostasis
Homeostasis and thermoregulation
homolytic fission
Hormonal communication
Hormonal communication 5.1.4
Hormonal control
human
Human Interactions
Human Interactions Case Studies
Human Rights
Human Rights Law
Ibsen and Rossetti
ICT Cambridge Technicals Level 3 - Unit 43 Understanding Social Media For Business - P1 M1 D1
Ideal gases
IGCSE History 4: Germany Depth Study
IGCSE History: The Gulf
Immunity
Imperial Image
Individuals with additional needs
Inequalities
Inequality
Inorganic and physical chemistry
Input, Output and Storage
Inteernational Relations - Interpretations
Integration
International Relations
International Relations 1918-1939
International Relations: the changing international order 1918—2001
Internet Marketing
Intoxication
Intro to Nursing
Introduction to the principle of superposition
Introduction to business
Introduction to Business Law
Introduction to economics and it\\\'s braches
Introduction to Homeostasis
Introduction to Microeconomics
Introduction to negligence and tort law
introduction to OP-AMP
Invention of the Barbarian
Investigative skills
Islam
Issues in Mental Health
IUPAC nomenclature
J560-05)
Java for beginners
Justice
Kachru’s Circles
Kantian Ethics
Kidney
Kinetics
Knowledge of God\\\'s existence
Knowledge of God\\\\\\\\\\\\\\\'s existence
Lab report 9 chem 2021
Landscape Systems
Language, Classical Greek
Law Making
Law Paper One
Law Reform
Lay People
League of Nations
Legal Personnel
Legal system
Liberation theology and marx
Light Dependent and Light Independent Reactions
Limiting factors of photosynthesis Summary
Lipids
literature
literature and film
Literature post-1900
LO1 Government Departments
LO1 NGB\\\'s
looking after teeth
Love and Relations
Love and Relationships
LPC and LLM Course Structure at BPP
M/506/2562
Macro
Macroeconomics
Madhyamaka & Prajnaparamita
Making places changing spaces
Management Accounting
Manganate redox titration
Manipulating genomes
Manipulating Genomes 6.1.3
Market structures
Mass Spectrometry
Mass Spectroscopy, Infrared Spectroscopy, NMR
Materials
math
MATHEMATICS A
Max for Live
Mechanics
Mechanics Minor
mechanisms
Media
Media Messages
Medical imaging
Medicine
Meditation
meiosis
Membranes
Mental Capacity Defences
Meta Ethics
Metaethics
Microeconomic introduction
Microeconomics
Microeconomics topics 1.1,1.2 and 2.1
Microscopy
Microscopy and cell structure
Mid-Tudor Crisis
MIDI & Audio Sequencing
Migration
Mind, Body and Soul
Misrepresentation
Mitosis
Mitosis and Meiosis
Mixed
Mock Questions
Model Essays
Modern Times
Module 1
Module 1 : Practical Skills in Physics
Module 2
Module 2 - Biological Membranes
Module 2 - Biological Molecules
Module 2 - Cell Division, Cell Diversity, and Cell Differentiation
Module 2 - Cell Structure
Module 2 - Enzymes
Module 2 - foundations in biology
Module 2 - Foundations in chemistry
Module 2 - Nucleotides and Nucleic Acids
Module 2 – Foundations in biology
Module 2 – Foundations in chemistry
Module 2 : Foundations in Biology
Module 2 : Foundations of Physics
Module 2 Foundations in Chemistry
Module 2- Cell Structure
Module 2,3 and 4
Module 2: Foundation in Chemistry
Module 2.1 Microscopy
Module 2.1.1 chapter 2 Foundations in Biology
Module 3
Module 3 - Biological molecules
Module 3 - core organic chemistry
Module 3 - Periodic table and energy
Module 3 : Forces & Motion
Module 3 Periodic Table and Periodicity
Module 3, Module 6 - organic chemistry
Module 3: Flashcards
Module 3: Forces and Motion
Module 3: Forces in action
Module 3: Periodic table and energy
Module 3.1.1 Chapter 7 Periodicity
Module 3.1.2 Chapter 8 Reactivity Trends
Module 3.2.1 Chapter 9 Enthalpy
Module 3.2.2 Chapter 10 Reaction Rates
Module 4
Module 4 - Core organic chemistry
Module 4 - Enzymes
Module 4 : Electrons, Waves and Photons
Module 4 Core Organic Chemistry
Module 4, Chapter 11
Module 4: Biodiversity, evolution and disease
Module 4: Electrons, waves and photons
Module 4: Organic Chemistry
Module 4.1.3 Chapter 13 Alkenes
Module 4.2.1 Chapter 14 Alcohols
Module 4.2.2 Chapter 15 Haloalkanes
Module 4.2.4 Chapter 17 Spectroscopy
Module 5
Module 5 - Communication, Homeostasis and Energy
Module 5 - Physical chemistry
Module 5 - Physical chemistry + transition metals
Module 5 - Physical chemistry and transition elements
Module 5 : Newtonian World and Astrophysics
Module 5: Newtonian World and Astrophysics
Module 6
Module 6 - Organic chemistry and analysis
Module 6 : Particles and Medical Physics
Module 6- Organic syntheis
Module 6- Organic synthesis
Module 6, Carbonyls and Ketones
Module 6: Particles and Medical Physics
Module 6.1.2 — Electrophilic Substitution
Module: 2,3,4,5 and 6 Mark Scheme Keywords
modules 1-4
Modules 1-6
Modules 1,2,3,4
Modules 2, 3, and 5
modules 4,5,6
Motion
Music
Music Technology
Mycenae
Napoleon
Natural Law
Nature of Law
NEA
NEA - Programming Project
needs wants and aspiration unit 2 topic 1 ceFS
Negligence
Negligence - Duty of Care
Neuronal Communication
Neuronal Communication 5.1.3
Neurones
Newspapers in depth study
Non British Depth Study: American Revolution
Non British Study
Non-Fatal Offences
non-specific & specific defences against pathogens
Novel
Novels
Nuclear and Particle Physics
Nucleic Acids
Nucleotides & Nucleic Acids
Nucleotides and Nucleic Acids
Nuisance
Occupiers Liability
OCR
OCR A HIGH DEMAND QUESTIONS
OCR A Level Biology C1. Cell Biology
OCR A Level Biology C2. Biological Molecule
OCR A Level Biology C4. Animal tissue , organ
OCR A Level Biology C5. Biological Membrane
OCR A Level Biology C6. Cell Division
OCR A Level Biology Revision Cards
OCR A LEVEL ENGLISH 2023
OCR A LEVEL JUNE 2022 CHEMISTRY A PAPER 2
OCR A LEVEL JUNE 2022 CHEMISTRY A PAPER 3
OCR A LEVEL MATHEMATICS
OCR A LEVEL MATHEMATICS MATHS B
OCR AS ENGLISH 2023
OCR AS LEVEL BIOLOGY A PAPER 1 June 2022 MS
OCR AS LEVEL BIOLOGY B PAPER 2 H022/02
OCR AS LEVEL JUNE 2022 CHEMISTRY A PAPER 2
OCR AS LEVEL JUNE 2022 CHEMISTRY B PAPER 2
OCR biology module 1
OCR GCE A LEVEL COMPUTER SCIENCE
OCR GCE A LEVEL COMPUTER SCIENCE PAPER 2 H446/02
OCR GCE AS LEVEL BIOLOGY A MS
OCR GCE AS Level Chemistry A H032/01 Breadth
OCR GCE Biology A H420/03: Unified biology Advanced GCE Mark Scheme for November 2020
OCR GCE Law H415/01: The legal system and criminal
OCR GCSE Economics topics 1.1,1.2 and 2.1
OCR Geography
OCR love and relations
OCR Year 2 A level Physics
offences against a property AO1
Official OCR 2023 Paper 3
OG0-093 PDF Dumps
Olympics and Global events
Ontological Argument from Reason
Operating Systems and Programming Languages
Organelles
Organic Basics
Organic chemistry
Organic Chemistry - MODULE 4 & 6
Organic Chemistry and Analysis
organic pathways
Organic reactions
Organic Synthesis
Organic synthesis chapter 18
Organic, Physical
Oscillations
Overview
Ownership analysis
Ozone
PAG 12 Respiration Rate of Yeast
PAG 12.1
Paper 1
paper 1
Paper 1 + Paper 2
Paper 1 Section B
paper 2
Paper 2 - Law Making and Law of Tort
PAPER 2 SECTION B: Occupiers Liability
paper 3
Paper 3 origins of the Cold War 1945-49
Paper 3: Mental health
Paper and markscheme
Paper One
papers and ,markschemes
past paper
Patterns of Inheritance
Patterns of Inheritance 6.1.2
PCR Summary
Period Table and Energy
Periodicity
Philosophy
Philosophy & Ethics
Philosophy and Ethics
Philosophy of Religion
Philosophy to religion
Photosynthesis
Photosynthesis 5.2.1
Photosynthesis and Respiration
physical
Physical chem
Physical Chemistry
Physical Chemistry - MODULE 3 & 5
Physical Chemistry and Transition Elements
Physical Education
Physical Geography
Physical Systems
Physical Systems Case Studies
Physics
PHYSICS 9702
Physics paper 1 2019 H556/01
Physiology
Plant & Animal responses 5.1.5
Plant and animal responses
Plant Responses
Plant Responses Summary
Plant transport
Plasma Membranes
Plato
Pluralism and Theology
Poems and Plays: Othello and William Blake
Poetry
Politics of the Late Republic
Polymers and life
Polymers, Amino Acids and Amides
Popular Culture & the Witchcraze
Population & Sustainability 6.3.2
Populations and sustainability
Populations and Sustainability Mind map
Power and Borders
Powers and Borders
Practical - EAPI
Practical Assessments
Practical EAPI
Practical Endorsement
Practical Endorsement GCE Biology
Practical Techniques
Problem of Evil
Product Design Coursework
Programming Project
Proof
Property Offences
Prose
Proteins
Provide support to manage pain and discomfort
Psychological factors
Psychological themes through core studies
Psychological: Skill acquisition
psychology
Psychology H567/03: Applied psychology
Psychology H167/02: Psychological themes
Pure
Pure mathematics
Quantum Physics
Quantum Physics- the photoelectric effect
R001 - Understanding computer systems
R005 - Creating an interactive product using multimedia components
R011 - Understanding technology - a project approach
R061 - Introduction to business
R062 - Planning for work
R108 - 3D design realisation
Radioactivity: Nuclear Fission and Fusion
Rates of Reaction
Reaction rates and equilibrium - module 10
Reactions
Reading as a writer, writing as a reader
Redox and Electrode Potentials
Religion and Ethics
religion and society
Religious Ethics
Religious Experience
Religious pluralism and society
Religious pluralism and theology
Religious Studies
Remedies
Research Methods
Research methods & Goobalisation
Research methods and researching social inequality
Researching and understanding social inequalities
Resistant Materials
Respecting Care services
Respiration
Respiration 5.2.2
restitution
Revision
Revision Guides
Revision Mock Paper
Revision Mock Paper Mark Scheme
Rossetti and Ibsen
Russia 1645—1741
Russia 1894-1941
Russia 1894–1941 - Unit Y21
Russia and it\\\'s Rulers
Russia and Its Rulers
Russia and Its Rulers 1855 to 1964
Russia and its rulers 1855-1964
Russia and its Rulers 1855—1964
Russia and its Rulers 1894-1941
Russian and its rulers
Rylands v Fletcher
Samsara
Scalar and vector quantities
science biology
Sentencing
Sexual ethics
Sexual reproduction in plants
Shakespeare
Significant Figures, Prime Factor Decomposition, Multiplying Brackets, Factorising Expressions, Indices, Pie Charts, Drawing Pie Charts, Solving Equations & Word Problems, Stem and Leaf Diagrams
Situation Ethics
Skill Acquisition
SLR 1 - 10
Social Groups
Social Psychology
Socialisation, Culture and Identity
socialisation, culture and identity- section A
Socio-Cultural
Sociocultural Factors
Solicitors, Barristers and Legal Executives
Soul mind body
space vs place
Spanish Writing
Species diversity
Specific immune response- communicable diseases
Sport and Exercise Psychology
sport psychology
Sports injuries and rehabilitation
Sports Organisations and Development
Sports Psychology
Stages in respiration summary
Stars
Statistics
Statistics Minor
Statutory Interpretation
Stonebridge Natural Science Pathway
Stresemann Essay
Strict Liability
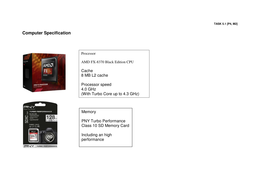
Structure and Function of Processor
Structure and properties of water
Studio Production
Succession Summary
Summary notes
Summary of Topics
Syntheses Reaction Map
Synthesis & Sampling
Synthetic Routes and Mechanisms
System Software and Operating Systems
Taking Refuge
technology
The Aeineid
The Aeneid
The Bloody Chamber and Other Stories
The Buddha
The Businesss Environment
The cell cycle: Meiosis and Mitosis
The challenge of secularism
The Changing Nature of Warfare
The characteristics of computing
The chemical industry
The Cold War
The Cold War in Europe
The Criminal Justice process.
The Crusader States in the 12th Century
The Crusades and the Crusader States
The Development of Mahayana Buddhism
The Duchess of Malfi
The Early Stuarts and the Origins of the Civil War
The Early Tudors
The Elizabethans
The First Crusade
The French Revolution
The Gothic
The halogens
The Iliad
The Judiciary
The Kidney
The Later Tudors
The Later Tudors 1547-1558
The legal system
The liver
The Merchant\\\'s Tale- Geoffrey Chaucer
the Middle East
The Middle East 1908–2011: Ottomans to Arab Spring
The Nature of God/Attributes of God
The oceans
The organisation and specialisation of cells
The Organisational Background to Business Administration The Management Framework to Business Administration
The pancreas
The person of Jesus Christ
The Problem of Evil
The Role of Markets
The Second Crusade
The Tempest- Part B essays
The Third Crusade
The Three Marks of Existence
The war of the roses - essay example
The World of The Hero H408/11
theft
Thematic study and historical interpretations
Themes Through Core Studies
thermal physics
Thursday 16 June 2022 – Morning A Level Psychology
Topic 1
Topic 1: Lifestyle Health and Risk
Topic 2 - The 1917 revolutions
Topic 3 - The civil war and Lenin
Topic 3.1 Climate Change
Topic 4 - Rule of Stalin
Tort law
Trade
Trade In the Contemporary World
Transition Elements
Transition Elements, Module 5
Transition Metals
translation
Transpiration
Transport in animals
Transport in Animals 3.1.2
Transport in plants
Transport in Plants 3.1.3
Tudor
Tudors
Tuesday 12 October 2021 – Morning A Level Chemistr
Twelfth Night
Types of Processor
U2 Researching + understanding social inequalities
U3 Debates in contemporary society
Understanding Health and Safety
Understanding Schizophrenia
unemployment
Unit 01 - Principles of anatomy and physiology in sport
Unit 02 - Sports coaching
Unit 05 - Communicating science
Unit 06 - Careers in science
Unit 07 - Food production
Unit 08 - Science of health
Unit 08 - Sport as a business
Unit 09 - Human behaviour
Unit 1
Unit 1 - Analysing media products and audiences
Unit 1 - Body systems and the effects of physical activity
Unit 1 - Building positive relationships in health and social care
Unit 1 - Communication in health and social care
Unit 1 - Fundamentals of IT
Unit 1 - Introduction to Advanced Mathematics
Unit 1 - Physical chemistry
Unit 1 - The business environment
Unit 1 C1 - Core Mathematics 1
unit 1 DEVELOPING EFFECTIVE COMMUNICATION IN HEALTH AND SOCIAL CARE
Unit 1.2
Unit 10
Unit 10 - Employer-employee relations
Unit 10 - Mechanics 2
Unit 10 - Nutrition for health
Unit 10 - Testing consumer products
Unit 11
Unit 11 - Accounting concepts
Unit 12
Unit 12 - Chemical design
Unit 12 - Financial accounting
Unit 12 - Mobile technology
Unit 12 - Promote positive behaviour
Unit 13
Unit 13 - Health and fitness testing for sport and exercise
Unit 13 - Management accounting
Unit 13 - Sexual health, reproduction and early development stages
Unit 13 - Social media and digital marketing
Unit 13 - Statistics 1
Unit 14
Unit 14 - Resource management
Unit 14 - Software engineering for business
Unit 14 - Statistics 2
Unit 14 - The impact of long-term physiological conditions
Unit 14 - Working in active leisure facilities
Unit 15
Unit 15 - Change management
Unit 15 - Promoting health and wellbeing
Unit 16
Unit 16 - Principles of project management
Unit 16 - Supporting people with dementia
Unit 16 Project Management
Unit 17
Unit 17 - Decision Mathematics 1
Unit 17 - Digital Marketing
Unit 17 - Internet of everything
Unit 17 - Responsible business practices
Unit 17 - Sports injuries and rehabilitation
Unit 17 - Supporting people with mental health conditions
Unit 18
Unit 18 - Caring for older people
Unit 18 - International business
Unit 18: Microbiology
Unit 19
Unit 19 Aim A,B
Unit 19 - Business events
Unit 19 - Computer systems - software
Unit 2
Unit 2 - Business Resources
Unit 2 - Concepts for Advanced Mathematics
Unit 2 - Equality, diversity and rights in health and social care
Unit 2 - Global information
Unit 2 - Sports coaching and activity leadership
Unit 2 - The Gothic
Unit 2 - Working in business
Unit 2 Assignment 1
Unit 2 P5
Unit 2.1
unit 2.1: changing places making spaces
Unit 20
Unit 20 - Being entrepreneurial - evaluating viable opportunities
Unit 20 - Business for engineering
Unit 20 - IT technical support
Unit 20 - Numerical Methods
Unit 21 - Looked after children and young people
Unit 21 - Maintenance
Unit 21 - Nutrition
Unit 21 - Web design prototyping
Unit 22 - Assessing risk in sport
Unit 22 - Further Pure Mathematics with Technology
Unit 22 - Psychology for health and social care
Unit 23 - complementary therapies
Unit 23 - Sociology for health and social care
Unit 23 Complementary Therapies for Health and Social Care
Unit 24 - Public health
Unit 25 - Music performance
Unit 25- Research methods
Unit 25- Research methods in health, social, child
Unit 29
Unit 3
Unit 3 - Business decisions
Unit 3 - Cyber security
Unit 3 - Exchange and Transport In Animals
Unit 3 - Health, safety and security in health and social care
Unit 3 - Methods for Advanced Mathematics
Unit 3 C3 - Core Mathematics 3
Unit 3 LAW03 - Criminal Law (Offences against the Person) or Contract Law
Unit 3.2
Unit 35 - Complementary therapies
Unit 35 - Social media products
Unit 37 - Understanding Business Ethics
unit 37- Understanding Business Ethics
Unit 4
Unit 4 - Anatomy and physiology for health and social care
Unit 4 - Applications of Advanced Mathematics
Unit 4 - Computer networks
Unit 4 - Customers and communication
Unit 4 - Development through the life stages
Unit 4 C4 - Core Mathematics 4
Unit 4 Computer Networks
Unit 4: Managing an Event
Unit 40 - UK film studies
Unit 5
Unit 5 - Anatomy
Unit 5 - Anatomy and physiology for health and social care
Unit 5 - Further Concepts for Advanced Mathematics
Unit 5 - Infection control
Unit 5 - International Business
Unit 5 - Marketing and market research
Unit 5 FP 1 - Further Pure Mathematics 1
Unit 5 learning aim A
Unit 5 Marketing and Market Research
Unit 6
Unit 6 - Application design
Unit 6 - Further Methods for Advanced Mathematics
Unit 6 - Marketing strategy
Unit 6 - Personal and Professional Development
Unit 6 - Personalisation and a person-centred approach to care
Unit 6 - Sociological perspectives
Unit 6 FP 2 - Further Pure Mathematics 2
Unit 6 personal and professional
Unit 7
Unit 7 - Data analysis and design
Unit 7 - Electrical devices
Unit 7 - Marketing campaign
Unit 7 - Practical Sports Performance
Unit 7 - Safeguarding
Unit 7 - Sociological Perspectives in Health and Social Care
Unit 7: Sociological Perspectives for Health and Social Care
Unit 8
Unit 8 - Creativity and activity for children and young people
Unit 8 - Introduction to human resources
Unit 8 - Project management
Unit 8 - Psychological Perspectives in Health and Social Care
Unit 8 M1 - Mechanics 1
Unit 8: Psychological Perspectives in Health
Unit 9
Unit 9 - Comics and graphic novel storytelling
Unit 9 - Mechanics 1
Unit 9 - Product development
Unit 9 - Recruitment and selection
Unit 9 - Supporting people with learning disabilities
Unit R021 - Essential values of care for use with individuals in care settings
Unit R022 - Communicating and working with individuals in health, social care and early years settings
Unit R023 - Understanding body systems and disorders
Unit R028 - Understanding the development and protection of young children in an early years setting
Unit R029 - Understanding the nutrients needed for good health
Unit Y106 The Early Tudors 1485-1558
Unit Y206 Spain 1469-1556
Unit Y209
Unit Y209 African Kingdoms c.1400–c.1800
Unit Y221 Democracy and Dictatorships
Unit Y318 - Russia and its Rulers
Unit Y321 The Middle East 1908–2011: Ottomans to A
Unit3: Health, safety and security
Units 1 to 4
Units 5 to 8
UNIVERSITY OF CAMBRIDGE LOCAL EXAMINATIONS SYNDICATE INTERNATIONAL EXAMINATIONS A’ LEVEL MANAGEMENT OF BUSINESS
USA 1919—1948: the people and the state
Variety
Various Modules
Vicarious Liability
Viruses
War of the Roses
Wars of the Roses
Water
Water and Carbon
Water and Carbon Cycles
Water potential
Waves
Web technologies
WGU C458
What’s in a Medicine?
WHOLE CONTENT
William Blake
William\\\'s Blake\\\'s Songs of Innocence and Experience
Women Civil rights 1865-1992
Women In Literature
World of the Hero
World of the Hero H408/11
writing
Y106 The Early Tudors
Y107/01 England 1547–1603: the Later Tudors
Y108 - The Early Stuarts 1603-1660
Y221 Germany
Y312/01: Popular culture and the Witchcraze
Y316, Britain and Ireland 1791-1921
Y319
Y320 From Colonialism to Independence 1857-1965
Y321
Y321: The Middle East 1908-1911; Ottomans to Arab
Year 1 Pure - Binomial Expansion
Year 1 Pure - Coordinate Geometry
Year 1 Pure - Differentiation
Year 1 Pure - Exponentials and Logarithms
Year 1 Pure - Graphs and Transformations
Year 1 Pure - Inequalities
Year 1 Pure - Integration
Year 1 Pure - Polynomials
Year 1 Pure - Quadratic Functions
Year 1 Pure - Surds and Indices
Year 1 Pure - Trigonometry
Year 1 Pure - Vectors
Year 1 and Year 2 content
Year 1 Pure
Year 2 Pure - Algebra
Year 2 Pure - Differential Equations
Year 2 Pure - Differentiation
Year 2 Pure - Functions
Year 2 Pure - Further Differentiation
Year 2 Pure - Integration
Year 2 Pure - Numerical Methods
Year 2 Pure - Parametric Equations
Year 2 Pure - Sequences and Series
Year 2 Pure - Trigonometric Functions
Year 2 Pure - Trigonometric Identities
Year 2 Pure - Trigonometry
Yeast PAG